
Independent Reference
The Definitive Resource on Ransomware
Fact-checked, continuously updated reference material on ransomware threats, prevention, and incident response. Written for security professionals, referenced by researchers, and available to everyone.
Ransomware in context: In 2024, ransomware attacks caused an estimated $20 billion in global damages. The average cost of recovery, excluding ransom payments, exceeded $2.73 million per incident (Sophos, 2024). Attacks now target hospitals, schools, municipal governments, and critical infrastructure with increasing frequency. This resource exists to help organisations understand and defend against these threats.
Reference Material
Knowledge Base
In-depth, fact-checked guides covering every major aspect of ransomware. Each entry is reviewed for accuracy and updated as new threat intelligence becomes available.
What Is Ransomware
Ransomware is a category of malicious software that encrypts files or locks systems and demands payment for their release. First documented in 1989, it has since evolved into a multi-billion dollar criminal industry affecting every sector worldwide.
Read full reference
Types of Ransomware
From crypto-ransomware and screen lockers to double-extortion schemes and Ransomware-as-a-Service (RaaS) platforms. A taxonomy of every known variant family and how they operate.

Prevention Strategies
Evidence-based measures for reducing ransomware risk: network segmentation, endpoint detection, backup architecture, patch management, email filtering, and employee security awareness training.

Incident Response Framework
A structured, step-by-step protocol for responding to an active ransomware event. Covers containment, eradication, forensic analysis, stakeholder communication, and post-incident review.
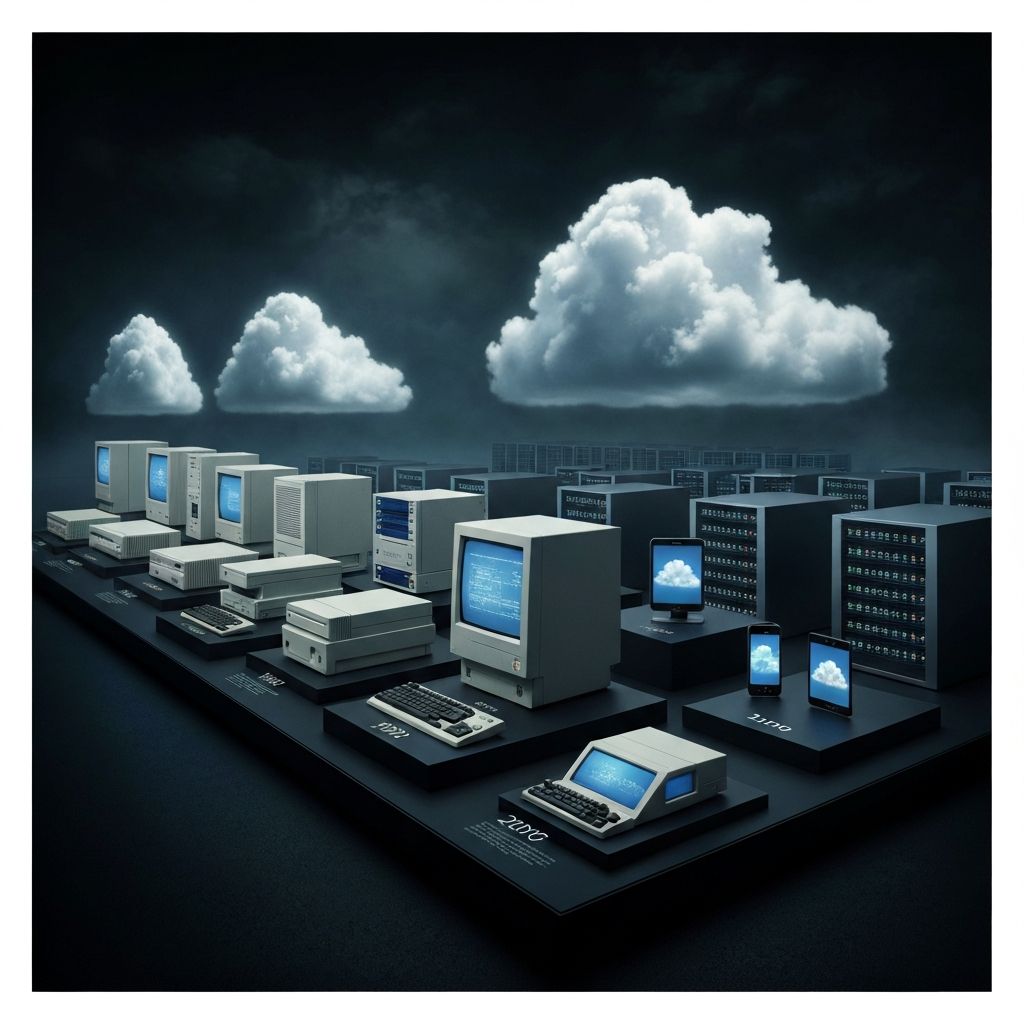
History and Timeline
From the 1989 AIDS Trojan distributed on floppy disks to the 2021 Colonial Pipeline shutdown, trace the full documented history of ransomware and the events that shaped today's threat landscape.
Research & Analysis
Recent Articles
Expert analysis on emerging threats, regulatory changes, and technical deep dives into the ransomware ecosystem.
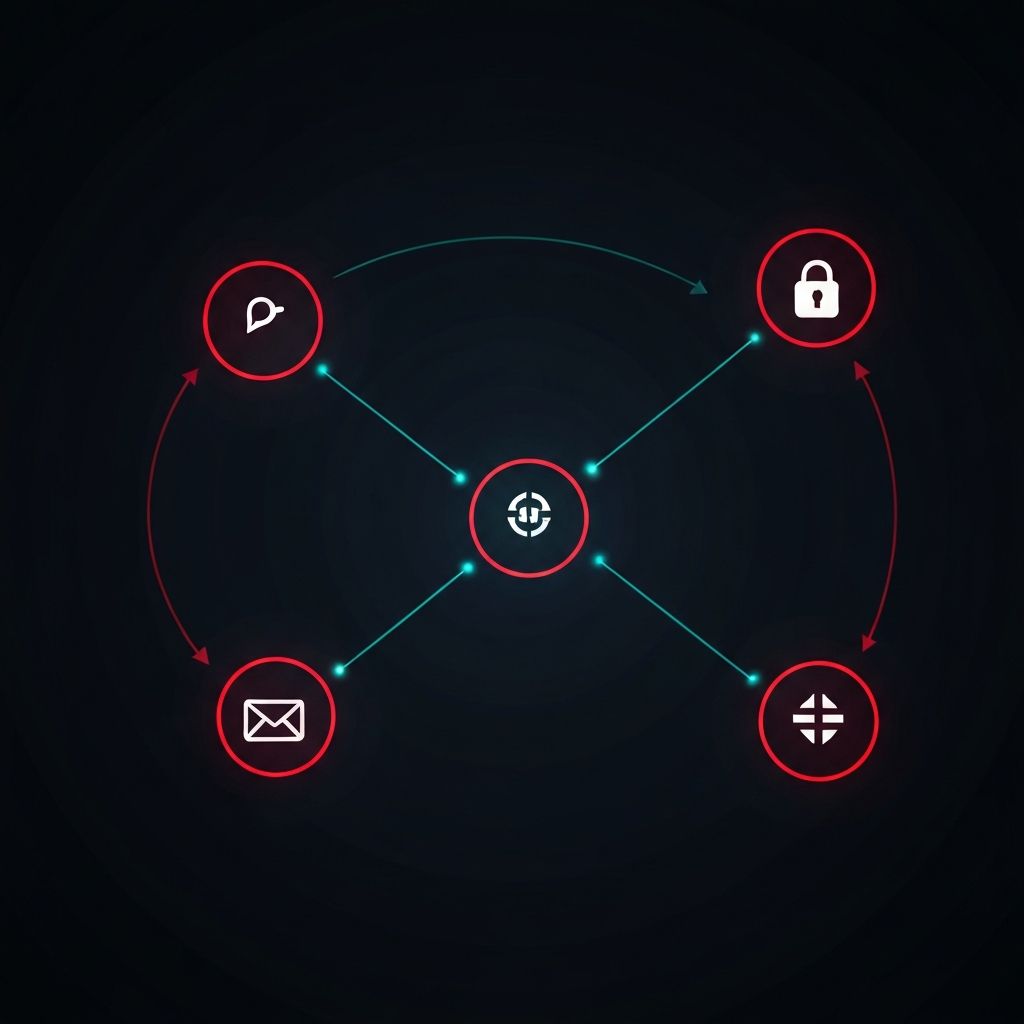
Understanding the Ransomware Attack Lifecycle
A stage-by-stage breakdown of how modern attacks unfold: initial access, persistence, lateral movement, data exfiltration, and encryption deployment.

NIS2 Directive: What European Businesses Must Know
The EU NIS2 Directive expands cybersecurity obligations to thousands of organisations. Key deadlines, penalties, and what compliance requires.

Recovery Without Paying the Ransom
Technical approaches endorsed by Europol and the FBI: backup restoration, free decryption tools, forensic data recovery, and memory analysis.
About This Resource
ransomware-protection.org is an independent, non-commercial educational project. All content is fact-checked against primary sources including law enforcement publications, peer-reviewed research, and threat intelligence from established cybersecurity organisations. We are not affiliated with any security vendor, and our editorial decisions are not influenced by commercial interests.
Are you a cybersecurity organisation?
Our partner directory connects security professionals with trusted vendors, MSSPs, and research institutions. Inquire about being listed.