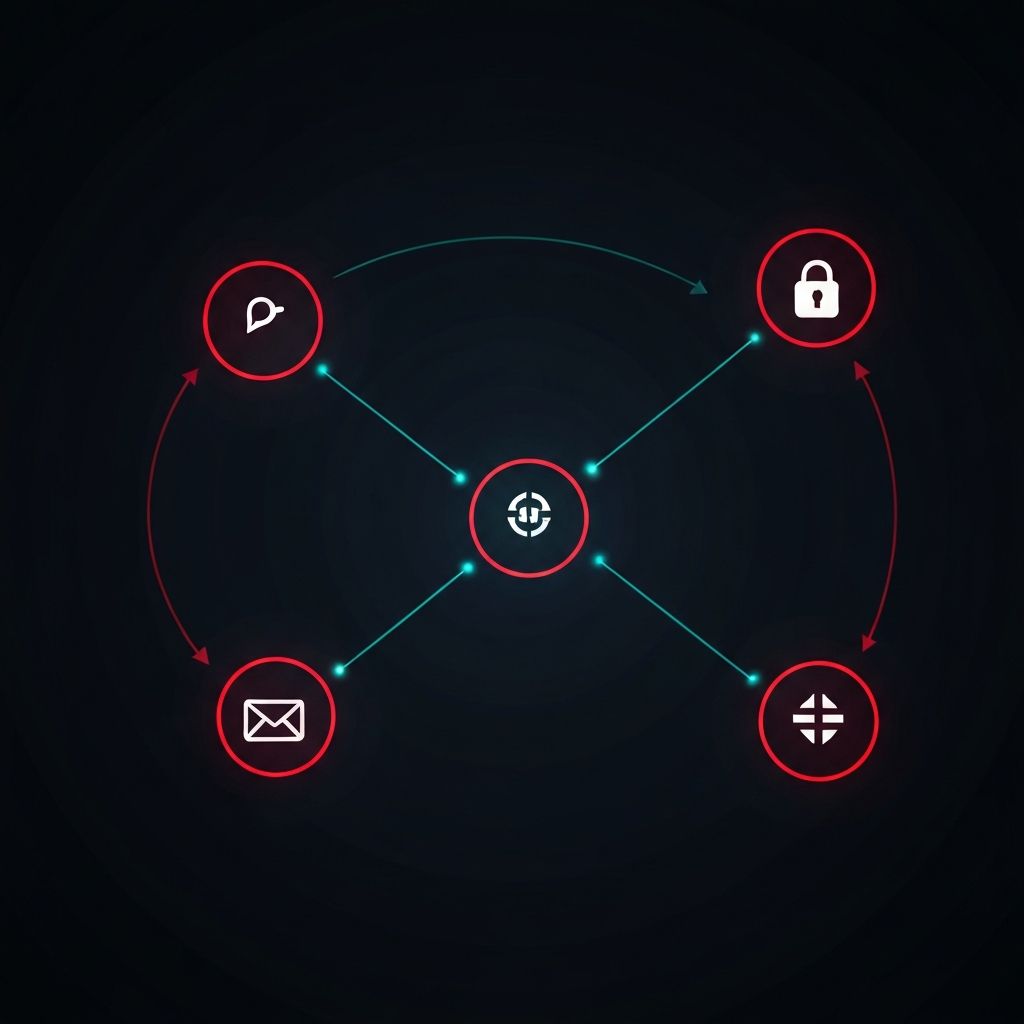
Understanding the Ransomware Attack Lifecycle: From Initial Access to Encryption
A detailed breakdown of how modern ransomware attacks unfold, from phishing emails and initial access brokers to lateral movement, data exfiltration, and final encryption.
The Evolution of Ransomware Attacks
Modern ransomware attacks bear little resemblance to the opportunistic, spray-and-pray campaigns of a decade ago. Today's threat actors operate with military precision, often spending weeks or months inside a network before deploying their encryption payload. Understanding this lifecycle is critical for building effective defenses.
Stage 1: Initial Access
The attack begins with gaining a foothold in the target network. The most common vectors include:
Phishing Emails: Despite decades of awareness training, phishing remains the single most effective entry point. Attackers craft highly convincing emails that impersonate trusted vendors, executives, or service providers, tricking employees into opening malicious attachments or clicking compromised links.
Exploiting Public-Facing Applications: Unpatched VPN gateways, web servers, and remote desktop services provide direct access to internal networks. The exploitation of known vulnerabilities in products like Citrix, Fortinet, and Microsoft Exchange has been responsible for some of the largest ransomware incidents in recent years.
Initial Access Brokers: A growing underground economy of initial access brokers (IABs) sells pre-existing access to compromised networks. Ransomware gangs purchase this access, significantly reducing the time and effort required to begin an attack.
Stage 2: Establishing Persistence
Once inside, attackers establish multiple persistence mechanisms to maintain access even if one is discovered. This includes creating new administrator accounts, deploying remote access tools like Cobalt Strike or AnyDesk, and scheduling tasks that re-establish connections after system reboots.
Stage 3: Lateral Movement and Privilege Escalation
The attacker moves through the network, harvesting credentials and escalating privileges. Tools like Mimikatz extract passwords from memory, while techniques like Kerberoasting target Active Directory to obtain domain administrator access. The goal is to reach the domain controller, which provides control over the entire environment.
Stage 4: Data Exfiltration
Before deploying ransomware, most modern groups exfiltrate sensitive data. This stolen data serves as additional leverage: even if the victim can restore from backups, the threat of publishing confidential information creates pressure to pay. Common exfiltration methods include cloud storage services, FTP servers, and encrypted tunnels.
Stage 5: Encryption and Ransom Demand
The final stage involves deploying the ransomware payload across as many systems as possible, often using Group Policy Objects (GPO) to push the malware through the domain. Backups are targeted first, then production systems are encrypted simultaneously. A ransom note appears, typically demanding cryptocurrency payment and directing victims to a Tor-based negotiation portal.
Where Defense Is Most Effective
The most cost-effective point of intervention is between stages 2 and 3. By this point, initial access has been gained, but the attacker has not yet achieved the domain-wide control needed for maximum impact. Robust network segmentation, endpoint detection and response (EDR) solutions, and regular credential audits can stop an attack in its tracks during this critical window.
Conclusion
Understanding the ransomware lifecycle transforms cybersecurity from a reactive discipline into a proactive one. Each stage presents opportunities for detection and disruption. Organizations that invest in layered defenses, regular monitoring, and incident response planning are far better positioned to prevent, detect, and recover from attacks.
Disclaimer: This article is provided for educational and informational purposes only. It does not constitute professional cybersecurity advice. Organizations facing an active ransomware incident should contact qualified incident response professionals and relevant law enforcement agencies.


